The Web’s Most Dangerous Neighborhood to Steer Clear!

Domain names are an important way to establish a unique identity, to assign names to numerically addressed Internet resources, and to make network moves possible (globally or locally via an intranet). A lot has changed since 1985, when the first domain Symbolics.com was registered, up until now that we have over 350 million domains in existence! Back then, what most consumers and businesses encountered were a small number of standard Top Level Domains (TLDs), such as .com, .net, .edu and .gov, as well as some country code domains like .fr (France), and .jp (Japan). In 2014, ICANN, the organization primarily behind the governance of the Internet, opened up the world to massive amounts of new gTLDs in response to requests from advertisers and domain speculators. With the explosion of new neighbourhoods on the web and the increasing adoption of the internet and smartphones, businesses and individuals rushed to secure their online identity. While these domains help us to share information, communicate, conduct business, entertain etc, they’re also susceptible to abuse by scammers and hackers seeking to profit from the same.
Some common abuses hurled by malicious entities are:
- Phishing: Domain names that support web pages which masquerade as a trustworthy entity such as a bank or online merchant, but are designed to “phish” for information or install malicious code.
- Malware: Domain names that facilitate the hosting and/or spreading of hostile or intrusive software that installs on end systems without the permission of the user. They can damage a system, steal data, or perform malicious activities on another computer.
- Botnet command-and-control: Domain names aiming to identify hosts that control botnets, which are collections of malware-infected computers that can be used to perpetrate various abusive activities such as denial of service, spam, etc.
- Spam: Domains that are advertised in unsolicited bulk email or used to name spam mail exchange systems. The term spam no longer describes only unsolicited bulk email but has become a major means of delivery for identifiers (domain names, hyperlinks, or addresses) used to support numerous security threats.
- Browser exploits: Attacks and malware that take advantage of vulnerable software.
- Risky affiliations: Sites with links that take the user to a malicious site and sites that have suspicious associations, such as their site ownership, registration, or hosting service.
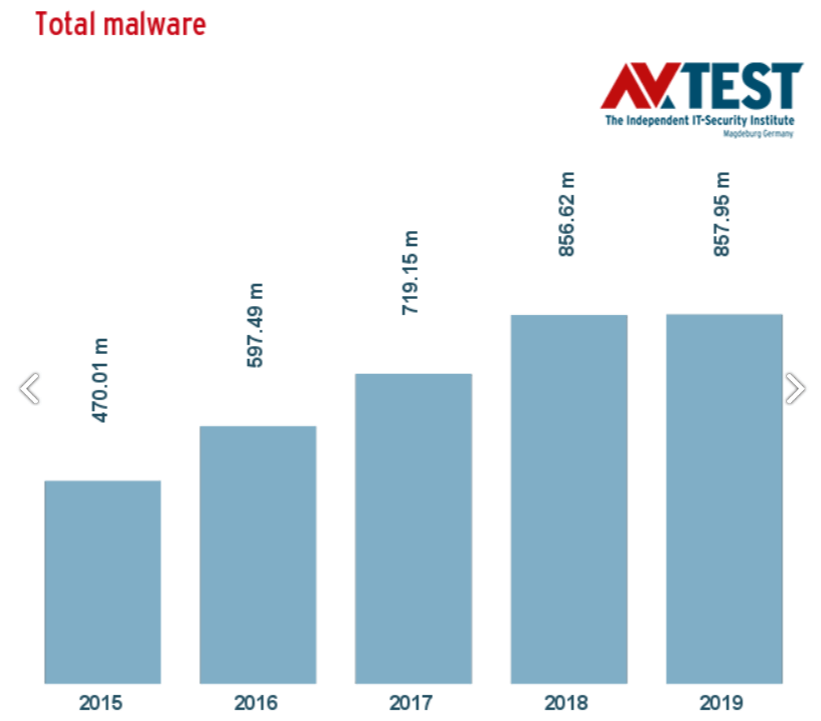
Source: https://www.av-test.org/en/statistics/malware
In the past 5 years, Malware has increased twofold!
This year, even more websites are going to contain malicious codes that steal passwords and identity information, take advantage of browser loopholes, disseminate malware, facilitate command and control (CandC) communications, send spam messages, host scam and phishing web pages, thereby causing a huge amount of loss to businesses as well as to individuals.

Source: http://www.surbl.org/tld
.com being the most popular and highly used TLD amounting to 43.57% of all existing TLDs, is obviously also a favourite for bad actors.
Some factors that affect how criminals pick a TLD:
- Lower Price — Cyber criminals prefer registrars with inexpensive registrations, volume discounts, and refund policies.
- Lack of Regulation — Cyber criminals prefer registrars with a no-questions-asked registration. The less information a scammer needs to provide, the better. Similarly, scammers prefer those registrars who act slowly, if at all, when notified of malicious domains.
- Ease of Registration — Cyber criminals prefer registrars that allow them to register in bulk. This is especially true of phishers and spammers who need large volumes of sites to offset a high rate of take-downs by TLD managers.
With ICANN opening up the world to new gTLDs beyond the 22 in 2014, the newer TLDs are popular among spammers and scammers alike because of their easy availability and low prices. At present, we have over 1,500 TLD’s; as the number of TLDs has increased, so have the opportunities for attackers.
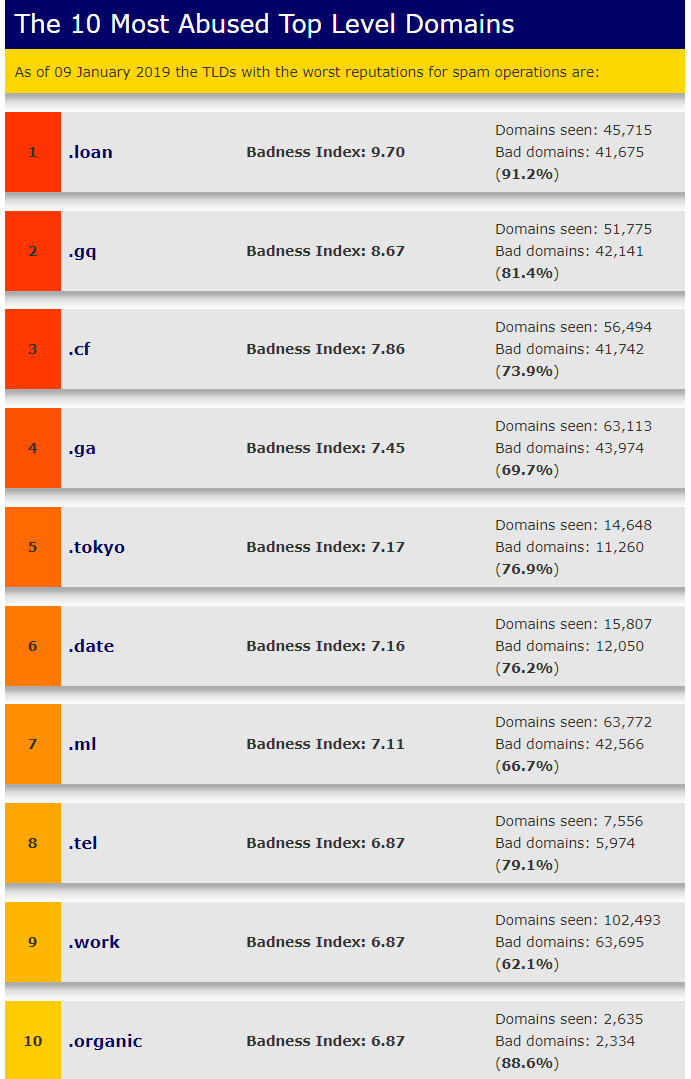
Source: https://www.spamhaus.org/statistics/tlds
.loan TLD at present has 91.1% domains tied to spam or malware dissemination (or both).
In order to keep up to date about domain name registrations across TLDs, security analysts can opt for Customized Reports on TLDs to help them analyse and prevent malicious entities before the damage is done!
Organizations and consumers can minimize their risks against bad TLDs:
- Businesses should consider blocking traffic that leads to risky TLDs. The blocking of all TLDs is obviously not the answer, but there may not be a justifiable business reason for your team to be browsing/accessing .party and .sex related sites. Block and filter where required.
- Misspelled domain names or popularly known online services containing domain ending with any of the above bad TLDs should also raise a red flag.
- Individuals should use caution to click on any links that contain dangerous TLDs if they encounter them in search results, e-mail, or social network environments.
- When dealing with a message from unknown entities, always hover the mouse over a link to help verify that it leads to the address displayed in the text of the link and don’t misdirect you.
- There is a big risk in using free hosting services, hence keeping away from them would be advisable.
- When choosing your domain name, watch out for what kind of domain extension you choose, and ensure you register it with a reputable domain name registrar. Avoid bad neighbourhoods to maintain your online reputation so as to not be blacklisted.
 Domain Name Stat
Domain Name Stat